Solutions
for Hosting
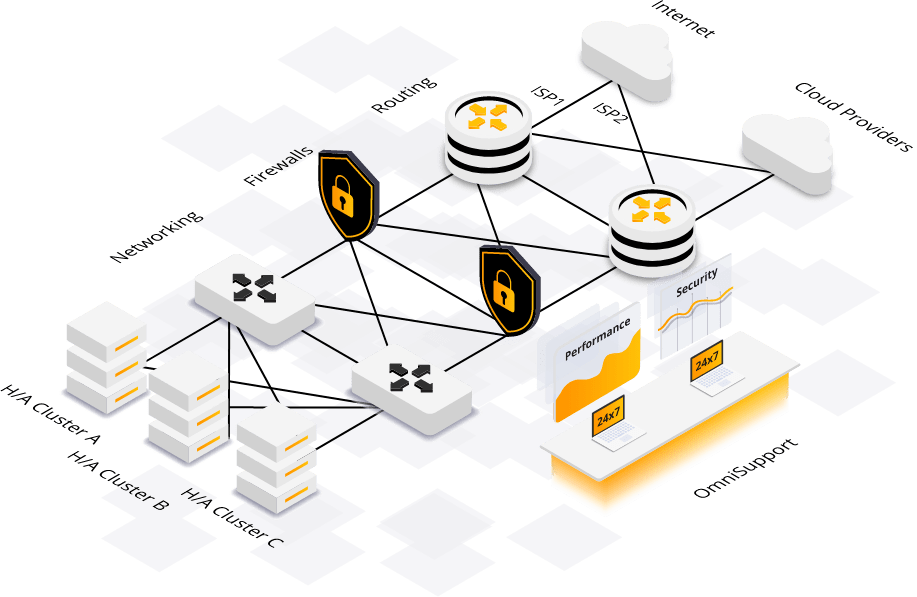
Fast, Reliable and Secure Hosting in our H/A Clusters.
Developers / Agencies
Friendly to develop PaaS and robust Private Clouds for Production.
Enterprises
Top Security, Reliability and Performance for Enterprises on Cloud or on Premises.
Government
Secure, High Performance, Ultra reliable GovCloud Solutions.
Partners / Resellers
Utilize MassiveGRID premium cloud services for your clients.